When programmers choose React Native as a platform for developing mobile apps, they search for benefits such as a single codebase for multiple systems, faster development, and TypeScript support. However, where is the most crucial aspect of application security? There are a lot of misconceptions about React Native app security floating around the internet.
App structure of React native:
For cross-platform programming, React Native offers an option. On iOS, the app uses native JavaScriptCore, whereas, on Android, JavaScriptCore libs are included in an APK.
A bridge is present to allow communication between the JavaScript engine and the application’s native components. When events occur in the native component of the program, they are converted into messages, processed, and then delivered to the JavaScript engine.
Ways to secure your React native application:
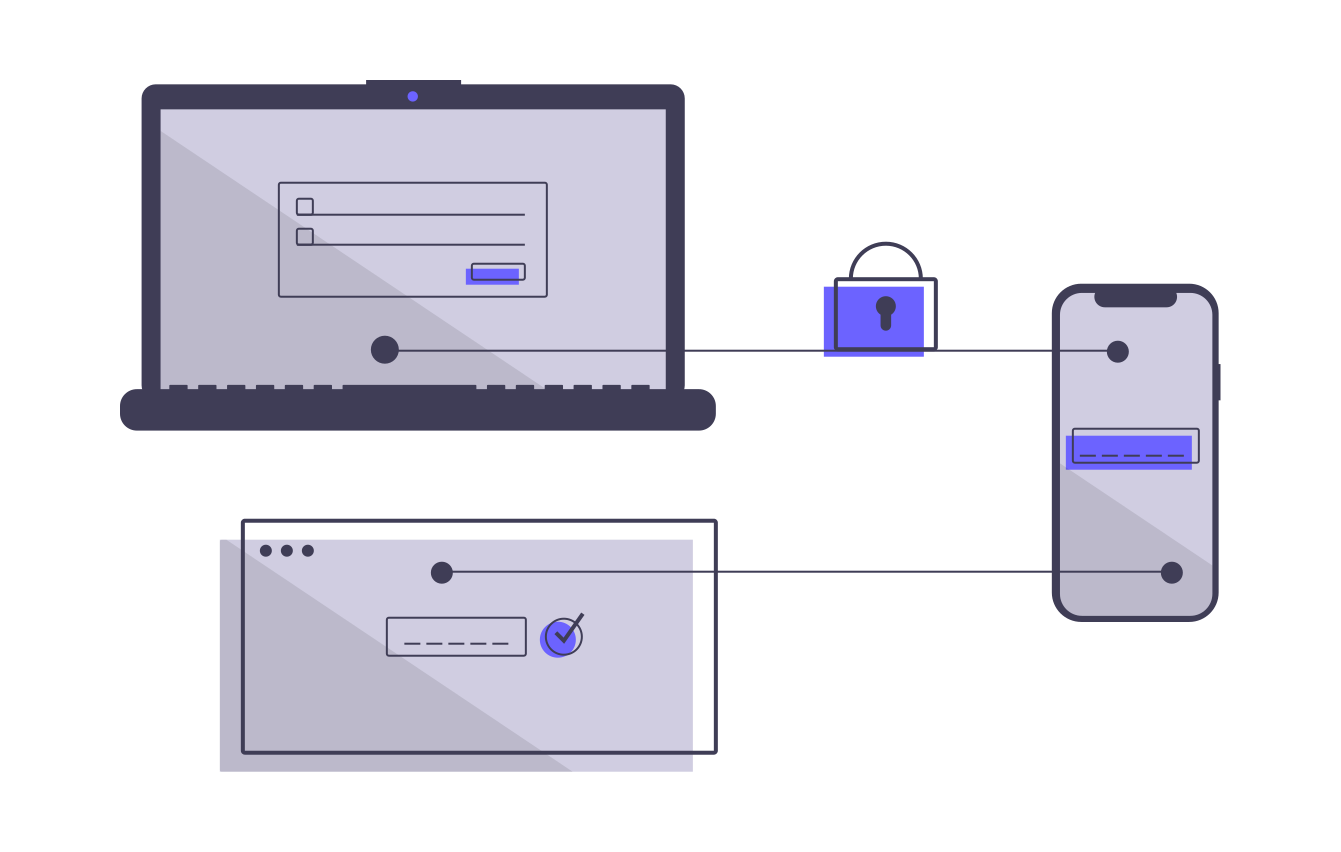
- Securing HTTP authentication: If your app has an identification function where users log in to establish an account, make sure it’s safe since client-side access controls are vulnerable to a variety of security risks that might compromise the app’s protocols.
Most notably, React Native Mobile App Development uses one of the following authentication methods: JSON Web Token, OAuth, AuthO, React Router, and PassportJs.
- Securing against DDOS: This security flaw often occurs when an application isn’t secure or has restrictions in disguising IP addresses. As a result, interacting with the server becomes harder, causing problems for services to function.
Here are some options for putting a halt to it:
- API rate limiting: Simply restrict the number of requests from a certain source to a specified IP. If you’re using Axios, there’s a full library called Axios-rate-limit.
- Add API limitations at the app level.
- Make server-side calls rather than client-side ones.
- Tests should be integrated to protect the application level.
- Jailbroken device detection: Use the following code to see if an iOS device is jailbroken. Create a React Native Native Module and integrate iOS code into your iOS project.
We’ll look for the following to see if there are any jailbroken devices. –
- Make sure Cydia is loaded.
- Check to see if the program has the ability to change system files.
- Check for unknown files.
- Check for additional dubious programs (FakeCarrier, Icy, and so on) that have been installed.
The Rootbeer library is useful for detecting rooted devices. Simply follow the installation instructions, and you may use the React Native Native Module to access Rootbear’s capabilities for detecting rooted devices. One can simply hire react native developers to help them with this framework.
Following the identification of Rooted Devices, the library will conduct a check.
- checkRootManagementApps
- checkTestKeys
- checkForDangerousProps
- checkForBusyBoxBinary
- checkForSuBinary
- checkSuExists
- checkForRWSystem
- checkPotentiallyDangerousApps
- checkRootCloakingApps
This is an Android-only API for detecting rooted phones and firmware unlocks. It also protects users from security risks, including device manipulation, rogue applications, and imposters.
The react-native-google-SafetyNet wrapper plugin, which is a SafetyNet API wrapper, may also be used to validate the user’s device. The react-native-device-info plugin may be used to check if an app is being used on a mobile device.
- Prevent forgery attacks: CSRF attacks are caused by the attacker’s integration of unauthorized cookies into the program or by unintentional cookies. It pushes users to perform undesirable actions while logged in to an online application.
- To manage sessions, use JWT tokens.
- Make sure your app only reads the CSRF tokens you’ve saved.
- With an authenticated request to the server, create necessary token headers.
- Protection against broken authentication: When the login information is input, the program fails, causing credential data to be leaked. Make sure you have the following items on hand to prevent it:
- Approval with many factors and two steps
- Granting access using cloud-based identification.
- Protect against components: When third-party libraries, modules, or APIs are utilized in a React project, there is always a risk. They undoubtedly aid us in the quick creation of features, but having your own set of security vulnerabilities may jeopardize your online application.
- Manually upgrade these libraries to the most up-to-date, secure, and stable versions.
- Replacing outdated versions of parts with new ones is also a good idea.
- Storage: Developers frequently need to save data locally, and async storage is sometimes used for storing Accesskeys, access-tokens, and user tokens. However, because AsyncStorage is unsecured storage, information may be extracted from it. React Native does not provide a secure data storage There are pre-existing solutions in iOS and Android, such as iOS Keychain and Android Keystore, which we are all familiar with.
Keys can be utilized for cryptographic operations once they’ve been stored in the Keystore, but the key material isn’t exportable. You may use the following NPM to utilize iOS Keychain & Android Secure Shared Preferences from React Native.
- Android security: Reverse engineering with an APK or app bundle file allows hackers to quickly gain access to our codebase. We can implement Pro Guard rules to prevent this. Your code is obfuscated by Pro Guard. As a result, if someone reverses engineers it, it will be unreadable, protecting you against engineering assaults. Pro Guard was also used to shrink the size of the APK by eliminating unnecessary code and resources. If your project includes a third-party library, you can use it.
- Ways of authentication: Nowadays, OAuth is increasingly often used for authentication between two applications that communicate with one other. How do servers know if a request is authenticated when it arrives? For you, OAuth 2.0 simplifies the authentication procedure. OAuth permits authentication using usernames and passwords rather than exchanging passwords.
React Native-based web apps are well-protected. It comes with its own set of costs and hazards. Follow the best practices of a safe web development lifecycle to make the app secure. Define and handle any threats, develop a security strategy, and design your security measures. Spend time developing a threat model for your online application since it helps to bring everything together.